Approaches for authenticating external applications in a machine-to-machine scenario | AWS Security Blog

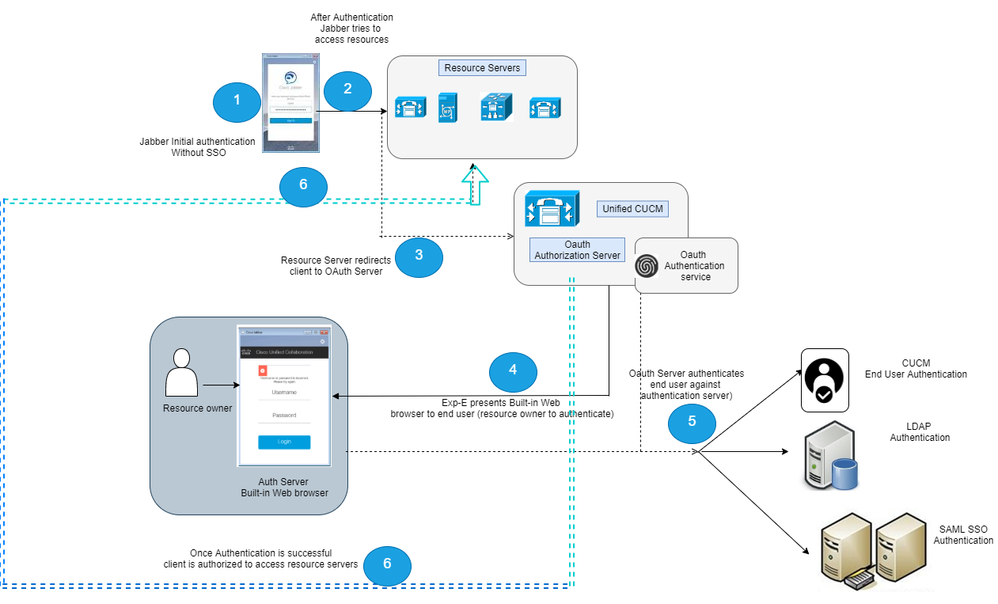
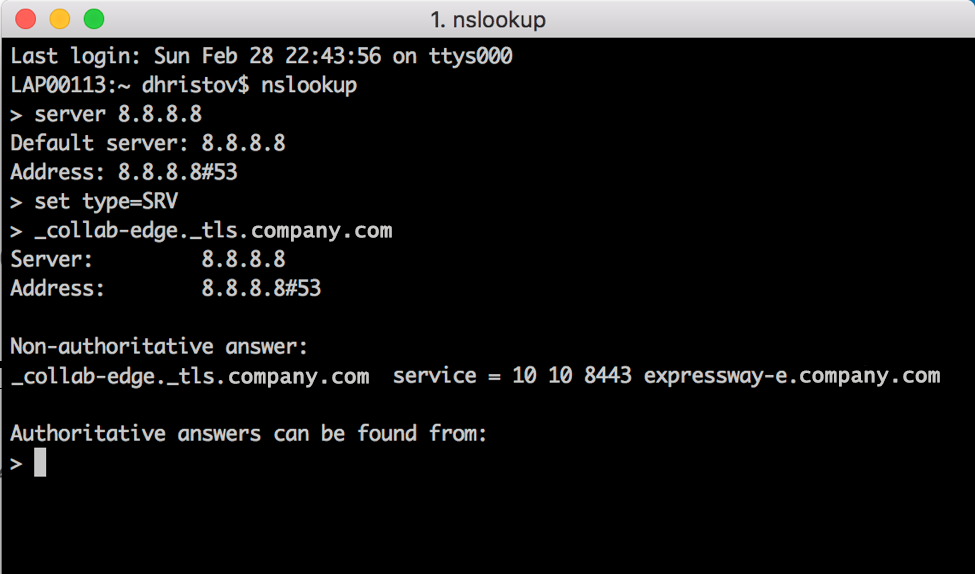
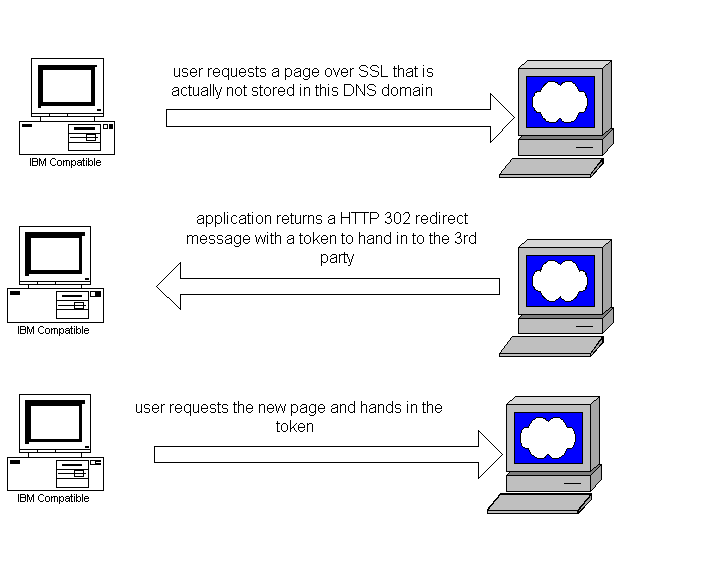
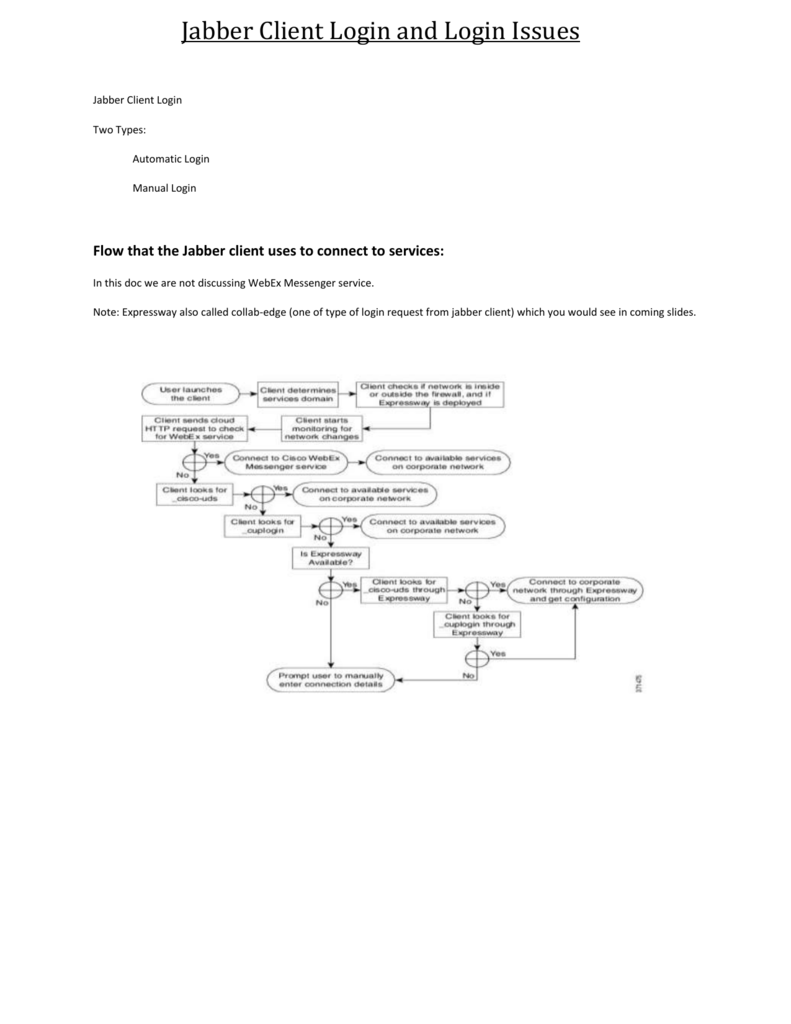
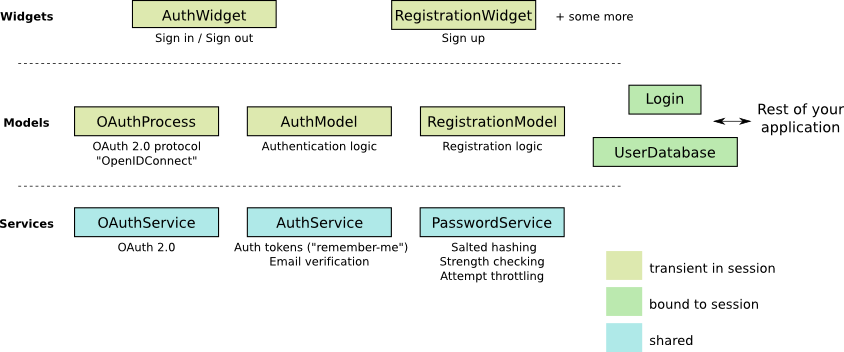
Understanding OAuth and MRA - Cisco Community | PDF | Communications Protocols | Security Technology

Understanding OAuth and MRA - Cisco Community | PDF | Communications Protocols | Security Technology

Understanding OAuth and MRA - Cisco Community | PDF | Communications Protocols | Security Technology

Understanding OAuth and MRA - Cisco Community | PDF | Communications Protocols | Security Technology